HTB Expressway Writeup – Full Walkthrough
A Hack The Box Expressway writeup focusing on network and system enumeration, uncovering hidden infrastructure, and privilege escalation through system misconfiguration.
HTB Expressway Writeup – Full Walkthrough
Info
- Target:
10.10.11.87 - Difficulty: Easy
- OS: Linux
Initial Recon
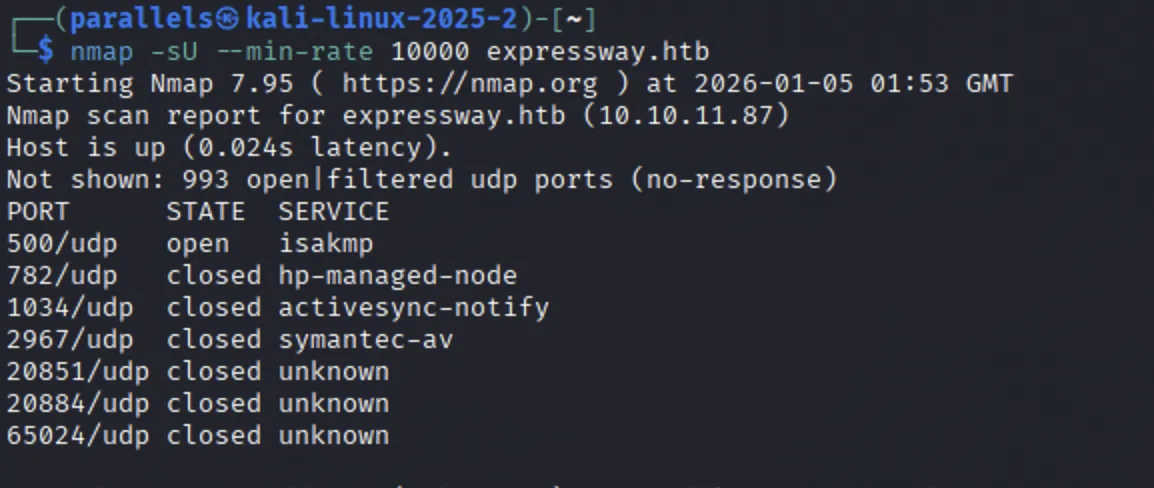
Ran my initial Nmap scan
1
nmap -sC -sV -oN nmap --min-rate 10000 expressway.htb
This, unfortunately, revealed nothing besides the ssh service running on port 21.
Thh next step was to try scan all of the host ports - perhaps there was some port obfuscation:
1
nmap -sC -sV -oN nmap_all_ports --min-rate 10000 expressway.htb
This didnt show any additional services.
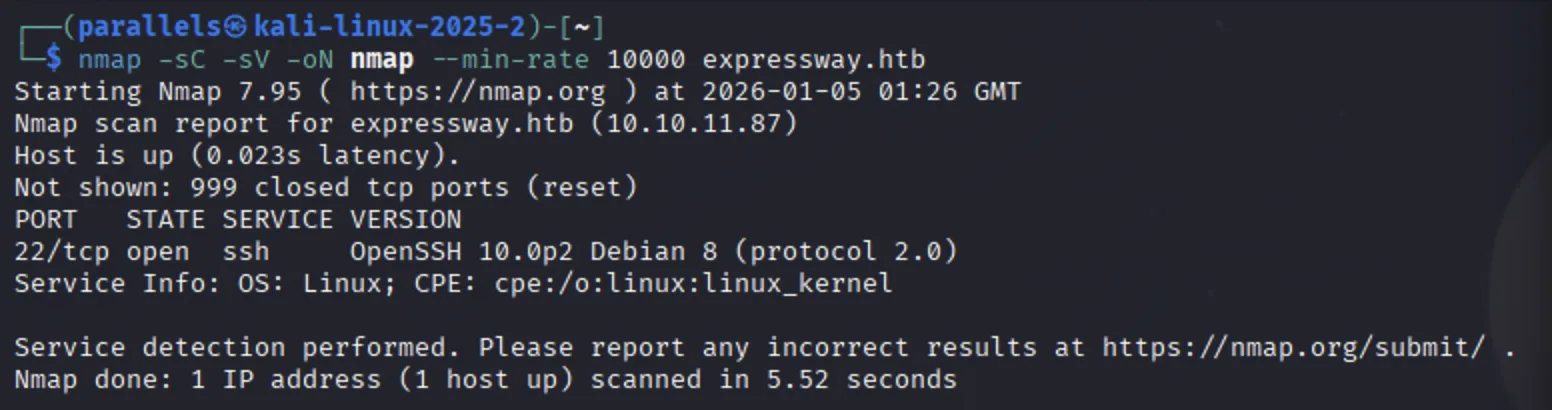
This leads to the services likely being run over the UDP protocol. I ran a UDP Nmap scan:
1
nmap -sU --min-rate 10000 expressway.htb
Oh no! This machine is still ACTIVE!
To adhere with Hack the Box’s community guidelines, the remainder of this post will be locked until the machine is retired.
Happy Hacking :-)
This post is licensed under
CC BY 4.0
by the author.