HTB MonitorsFour Writeup – Full Walkthrough
A Hack The Box MonitorsFour writeup covering web application enumeration, analysis of web-language weaknesses, and privilege escalation through a popular service's misconfiguration.
HTB MonitorsFour Writeup – Full Walkthrough
Info
- Target:
10.129.33.47 - Difficulty: Easy
- OS: Windows
Enumeration
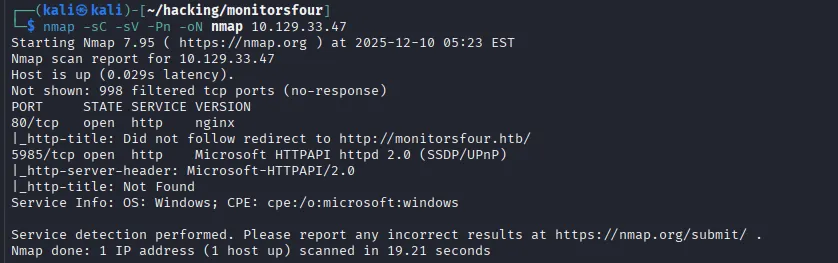
Initial nmap scan
1
nmap -sC -sV -Pn -oN nmap 10.129.33.47
Findings
- Port 80: http server - suggests a redirect to
http://monitorsfour.htb/- Looks like we need to add
monitorsfour.htbto the/etc/hostsfile in order to view this webpage.
- Looks like we need to add
- Port 5985: a HTTPAPI service, this could likely to allow us to make WinRM connections
- Useful if we gain some user credentials
Oh No! This Machine is Still Active!
MonitorsFour is currently ACTIVE on Hack The Box. To adhere with Hack the
Box’s community guidelines, the remainder of this post will be locked until the machine is retired.
For hints or discussion, join the community on the Hack The Box Discord.
Happy Hacking! 👾
This post is licensed under
CC BY 4.0
by the author.